我已经在Centos 7上运行了一个LDAP服务器.id,getent passwd,用户工作.但’ssh’失败了.从/ var / log / secure看来,身份验证似乎成功了,但是pam不喜欢其他东西.我不确定如何缩小问题所在.
在/ var /日志/安全:
May 11 16:33:40 localhost sshd[45055]: pam_unix(sshd:auth): authentication failure; logname= uid=0 euid=0 tty=ssh ruser= rhost=ldapserver.abc.com user=user1
May 11 16:33:40 localhost sshd[45055]: pam_sss(sshd:auth): authentication success; logname= uid=0 euid=0 tty=ssh ruser= rhost=ldapserver.abc.com user=user1
May 11 16:33:40 localhost sshd[45055]: pam_sss(sshd:account): Access denied for user user1: 6 (Permission denied)
May 11 16:33:40 localhost sshd[45055]: Failed password for user1 from ldapserver.abc.com port 55185 ssh2
May 11 16:33:40 localhost sshd[45055]: fatal: Access denied for user user1 by PAM account configuration [preauth]
/etc/sssd/sssd.conf:
[sssd]
services = nss,pam,autofs,ssh
config_file_version = 2
domains = default
[nss]
homedir_substring = /home
filter_users = root,ldap,named,avahi,haldaemon,dbus,radiusd,newsnsdc,nscd
[domain/default]
enumerate = False
ldap_tls_reqcert = never
autofs_provider = ldap
cache_credentials = True
krb5_realm = #
ldap_search_base = dc=abc,dc=com
id_provider = ldap
auth_provider = ldap
chpass_provider = ldap
access_provider = ldap
ldap_tls_cacert = /etc/openldap/certs/cacert.pem
ldap_uri = ldaps://ldapserver.abc.com:636
ldap_id_use_start_tls = False
ldap_default_bind_dn = uid=nssproxy,ou=users,dc=abc,dc=com
ldap_chpass_uri = ldaps://ldapserver.abc.com:636
ldap_default_authtok_type = password
ldap_default_authtok = 12345
debug_level = 4
[pam]
debug_level = 4
[sudo]
[autofs]
[ssh]
debug_level = 9
[pac]
[ifp]
/etc/pam.d/password-auth-ac:
#%PAM-1.0
# This file is auto-generated.
# User changes will be destroyed the next time authconfig is run.
auth required pam_env.so
auth sufficient pam_unix.so nullok try_first_pass
auth requisite pam_succeed_if.so uid >= 1000 quiet_success
auth sufficient pam_sss.so use_first_pass
auth required pam_deny.so
account required pam_unix.so
account sufficient pam_localuser.so
account sufficient pam_succeed_if.so uid < 1000 quiet
account [default=bad success=ok user_unknown=ignore] pam_sss.so
account required pam_permit.so
password requisite pam_pwquality.so try_first_pass local_users_only retry=3 authtok_type=
password sufficient pam_unix.so sha512 shadow nullok try_first_pass use_authtok
password sufficient pam_sss.so use_authtok
password required pam_deny.so
session optional pam_keyinit.so revoke
session required pam_limits.so
-session optional pam_systemd.so
session [success=1 default=ignore] pam_succeed_if.so service in crond quiet use_uid
session required pam_unix.so
session optional pam_sss.so
/etc/pam.d/system-auth-ac:
#%PAM-1.0
# This file is auto-generated.
# User changes will be destroyed the next time authconfig is run.
auth required pam_env.so
auth sufficient pam_fprintd.so
auth sufficient pam_unix.so nullok try_first_pass
auth requisite pam_succeed_if.so uid >= 1000 quiet_success
auth sufficient pam_sss.so use_first_pass
auth required pam_deny.so
account required pam_unix.so
account sufficient pam_localuser.so
account sufficient pam_succeed_if.so uid < 1000 quiet
account [default=bad success=ok user_unknown=ignore] pam_sss.so
account required pam_permit.so
password requisite pam_pwquality.so try_first_pass local_users_only retry=3 authtok_type=
password sufficient pam_unix.so sha512 shadow nullok try_first_pass use_authtok
password sufficient pam_sss.so use_authtok
password required pam_deny.so
session optional pam_keyinit.so revoke
session required pam_limits.so
-session optional pam_systemd.so
session [success=1 default=ignore] pam_succeed_if.so service in crond quiet use_uid
session required pam_unix.so
session optional pam_sss.so
/etc/nsswitch.conf中:
passwd: files sss
shadow: files sss
group: files sss
#initgroups: files
#hosts: db files nisplus nis dns
hosts: files dns
bootparams: nisplus [NOTFOUND=return] files
ethers: files
netmasks: files
networks: files
protocols: files
rpc: files
services: files sss
netgroup: files sss
publickey: nisplus
automount: files sss
aliases: files nisplus
最佳答案
sssd does not support authentication over an unencrypted channel
手册页中的这一行应作为答案专门发布.

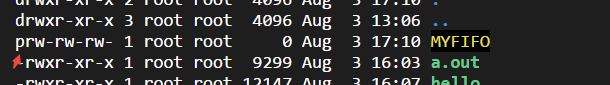 linux常用进程通信方式包括管道(pipe)、有名管道(FIFO)、...
linux常用进程通信方式包括管道(pipe)、有名管道(FIFO)、... Linux性能观测工具按类别可分为系统级别和进程级别,系统级别...
Linux性能观测工具按类别可分为系统级别和进程级别,系统级别...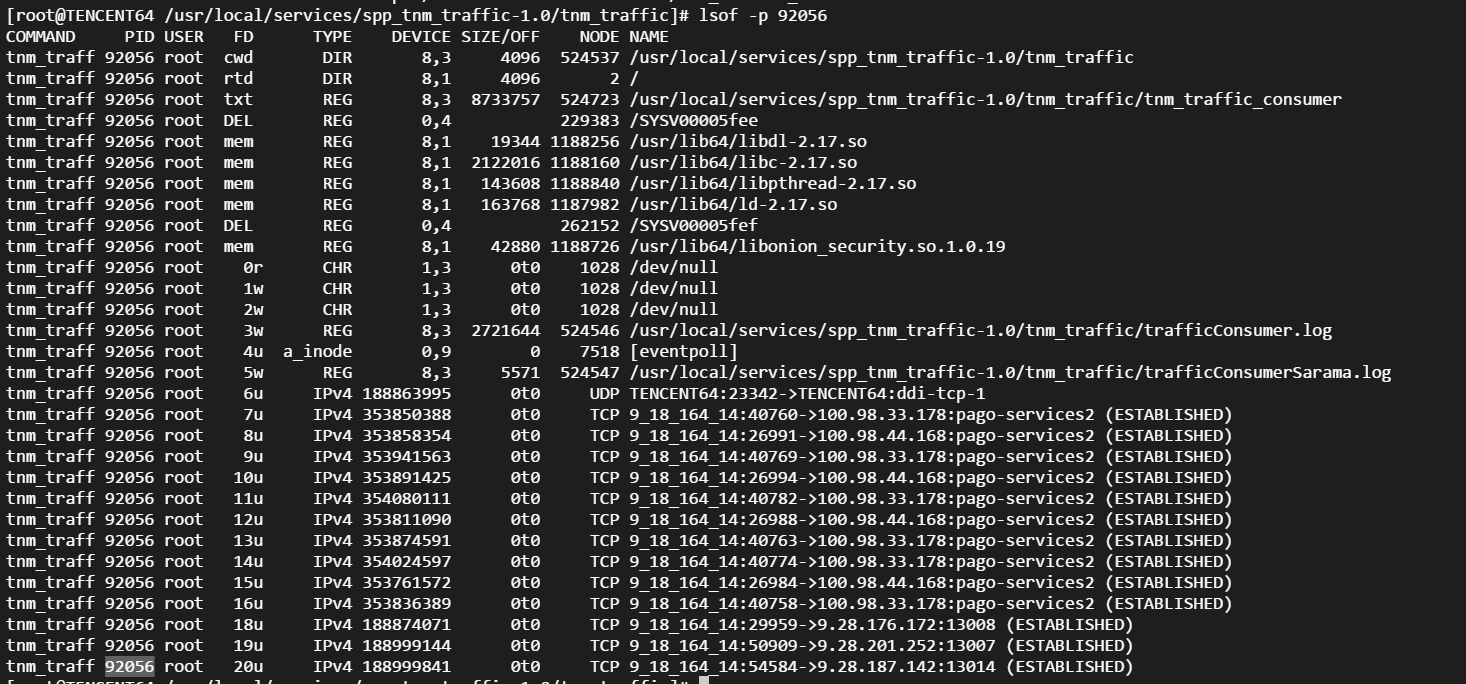 本文包含作者工作中常用到的一些命令,用于诊断网络、磁盘占满...
本文包含作者工作中常用到的一些命令,用于诊断网络、磁盘占满... linux的平均负载表示运行态和就绪态及不可中断状态(正在io)的...
linux的平均负载表示运行态和就绪态及不可中断状态(正在io)的... CPU上下文频繁切换会导致系统性能下降,切换分为进程切换、线...
CPU上下文频繁切换会导致系统性能下降,切换分为进程切换、线...