安装CFSSL
curl -s -L -o /bin/cfssl https://pkg.cfssl.org/R1.2/cfssl_linux-amd64
curl -s -L -o /bin/cfssljson https://pkg.cfssl.org/R1.2/cfssljson_linux-amd64
curl -s -L -o /bin/cfssl-certinfo https://pkg.cfssl.org/R1.2/cfssl-certinfo_linux-amd64
chmod +x /bin/cfssl*
容器相关证书类型
client certificate: 用于服务端认证客户端,例如etcdctl、etcd proxy、fleetctl、docker客户端
server certificate: 服务端使用,客户端以此验证服务端身份,例如docker服务端、kube-apiserver
peer certificate: 双向证书,用于etcd集群成员间通信
创建CA证书
生成默认CA配置
mkdir /opt/ssl
cd /opt/ssl
cfssl print-defaults config > ca-config.json
cfssl print-defaults csr > ca-csr.json修改ca-config.json,分别配置针对三种不同证书类型的profile,其中有效期43800h为5年
{
"signing": {
"default": {
"expiry": "43800h"
},"profiles": {
"server": {
"expiry": "43800h","usages": [
"signing","key encipherment","server auth"
]
},"client": {
"expiry": "43800h","client auth"
]
},"peer": {
"expiry": "43800h","server auth","client auth"
]
}
}
}
}修改ca-csr.config
{
"CN": "Self Signed Ca","key": {
"algo": "rsa","size": 2048
},"names": [
{
"C": "CN","L": "SH","O": "Netease","ST": "SH","OU": "OT"
} ]
}生成CA证书和私钥
cfssl gencert -initca ca-csr.json | cfssljson -bare ca -
生成ca.pem、ca.csr、ca-key.pem(CA私钥,需妥善保管)
签发Server Certificate
cfssl print-defaults csr > server-csr.jsonvim server-csr.json
{
"CN": "Server","hosts": [
"192.168.1.1"
],"key": {
"algo": "ecdsa","size": 256
},"ST": "SH"
}
]
}生成服务端证书和私钥
cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=kubernetes server-csr.json | cfssljson -bare server签发Client Certificate
cfssl print-defaults csr > admin-csr.jsonvim admin-csr.json
{
"CN": "Client","hosts": [],"ST": "SH"
}
]
}生成客户端证书和私钥
cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=kubernetes admin-csr.json | cfssljson -bare admin
签发peer certificate
cfssl print-defaults csr > kube-proxy-csr.json
vim kube-proxy-csr.json
{
"CN": "member1","hosts": [
"192.168.1.1"
],"ST": "SH"
}
]
}为节点member1生成证书和私钥:
cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=kubernetes kube-proxy-csr.json | cfssljson -bare kube-proxy针对etcd服务,每个etcd节点上按照上述方法生成相应的证书和私钥
最后校验证书
校验生成的证书是否和配置相符
openssl x509 -in ca.pem -text -noout
openssl x509 -in server.pem -text -noout
openssl x509 -in client.pem -text -noout
 最近一直在开发Apworks框架的案例代码,同时也在一起修复Apw...
最近一直在开发Apworks框架的案例代码,同时也在一起修复Apw... 最近每天都在空闲时间努力编写Apworks框架的案例代码WeText。...
最近每天都在空闲时间努力编写Apworks框架的案例代码WeText。... 在《Kubernetes中分布式存储Rook-Ceph部署快速演练》文章中,...
在《Kubernetes中分布式存储Rook-Ceph部署快速演练》文章中,...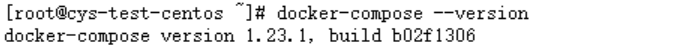 CentOS下Docker与.netcore(一) 之 安装 CentOS下Docker与.ne...
CentOS下Docker与.netcore(一) 之 安装 CentOS下Docker与.ne... CentOS下Docker与.netcore(一) 之 安装 CentOS下Docker与.ne...
CentOS下Docker与.netcore(一) 之 安装 CentOS下Docker与.ne...